Zero Trust by Design
Apply security at the infrastructure layer. Prevent misconfiguration and enforce governance from day one.

What is This?
Zero Trust operates on the assumption of breach. Every access request is verified, authenticated, and authorized based on dynamic policy. There is no implicit trust.
Network Isolation: Every project is network-isolated by default. Access between projects must be explicitly defined and authorized.
Lateral Movement Suppression: Segmentation is enforced at the infrastructure level to prevent ransomware propagation and lateral movement.
Containment: Multiple security layers are designed to isolate incidents, ensuring that a compromise in one segment does not impact the broader environment.
How Infrastream Enforces Zero Trust
Infrastream integrates seamlessly with your existing ecosystem - no rebuilds, no disruptions.
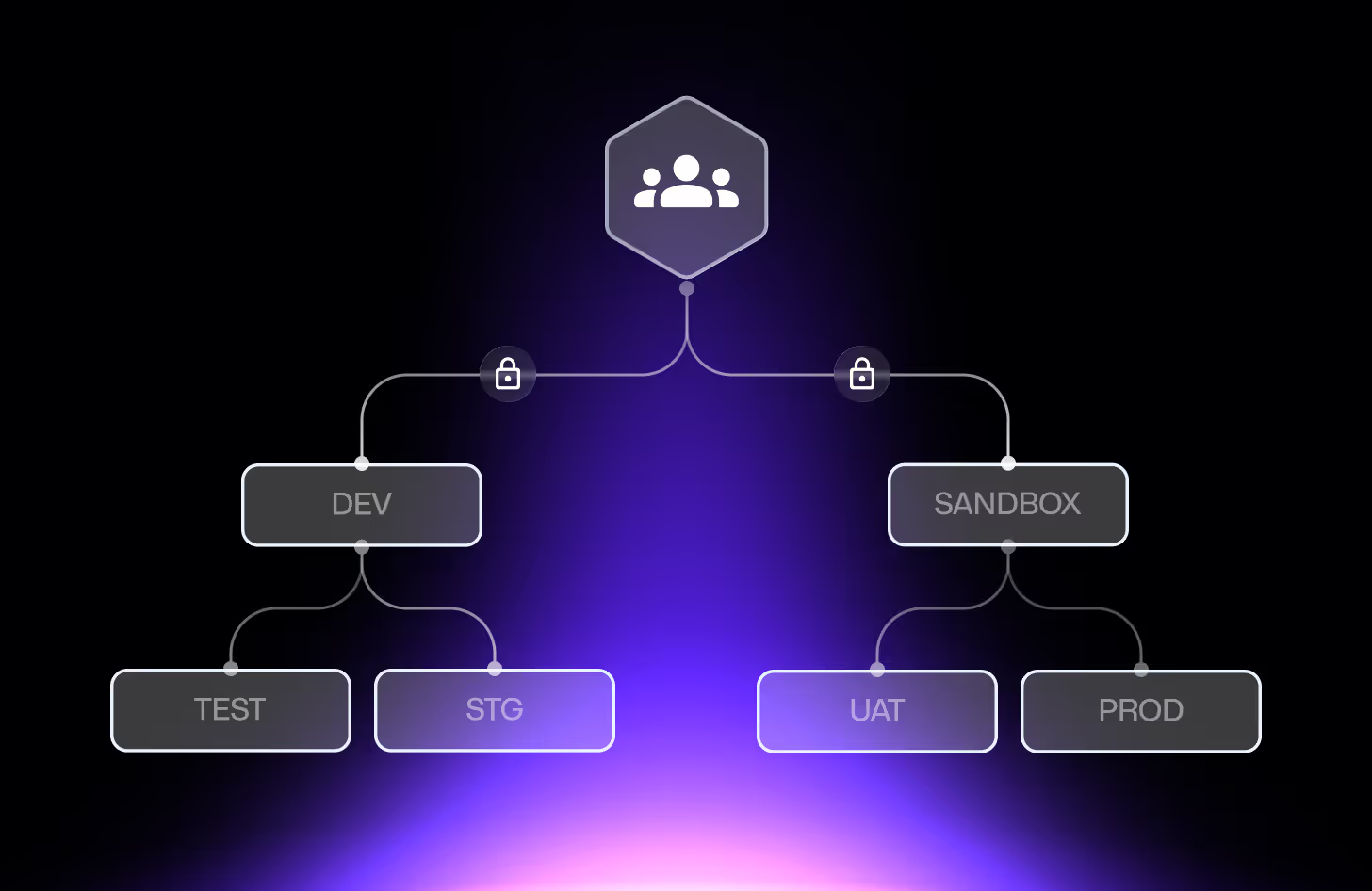
Microsegmentation That Actually Segments
Infrastream enforces project-level segmentation to prevent lateral threats. Every access exception is routed through a DevSecOps-approved pull request at the organization root—ensuring that even "breaks from the norm" are audited, peer-reviewed, and intentional.
Least Privilege, By Design
Access isn’t granted “just in case.” It’s provisioned just-in-time, scoped to the task, and logged every step of the way. Every session is unique, time-bound, and fully auditable, ensuring that the principle of least privilege is an operational requirement rather than a manual policy.

Identity-First Access for Agentic and AI Workloads
It’s about who you are and what you’re suppose to access. Every request is verified based on identity, role, behavior, and context, not just credentials.



Why This Matters
Traditional perimeter-based networks allow lateral movement once a breach occurs, creating high blast-radius risk. Infrastream mitigates this by enforcing a Zero Trust architecture where every project is isolated by default.
All connectivity exceptions are defined through a DevSecOps-approved pull request at the organization root, ensuring every security change is audited and peer-reviewed.
A single compromise stays contained instead of becoming a systemic failure.

